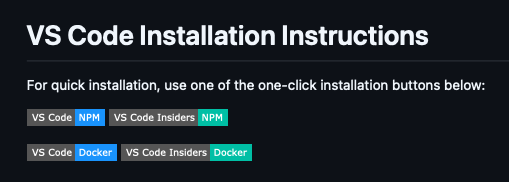
While browsing a GitHub repository recently, I noticed a feature with potential as a social engineering vector for payload delivery: a badge providing an almost single-click method to install an arbitrary Model Context Protocol (MCP) server directly from a README.md.
Further investigation confirms this is the documented and preferred method for distributing MCP servers.
Under The Hood
These badges simply link to insiders.vscode.dev/redirect/mcp/install using a specific schema:
https://insiders.vscode.dev/redirect/mcp/install?name=<NAME>&config={"command":"<COMMAND>","args":["<ARG1>","<ARG2>"]}